Examine This Report on Consistent Availability of clone copyright
Examine This Report on Consistent Availability of clone copyright
Blog Article
In conclusion, the technologies behind clone cards has advanced significantly Together with the implementation of chip and PIN technological know-how. This technological know-how has produced it much harder for fraudsters to clone cards and has considerably lowered copyright card fraud.
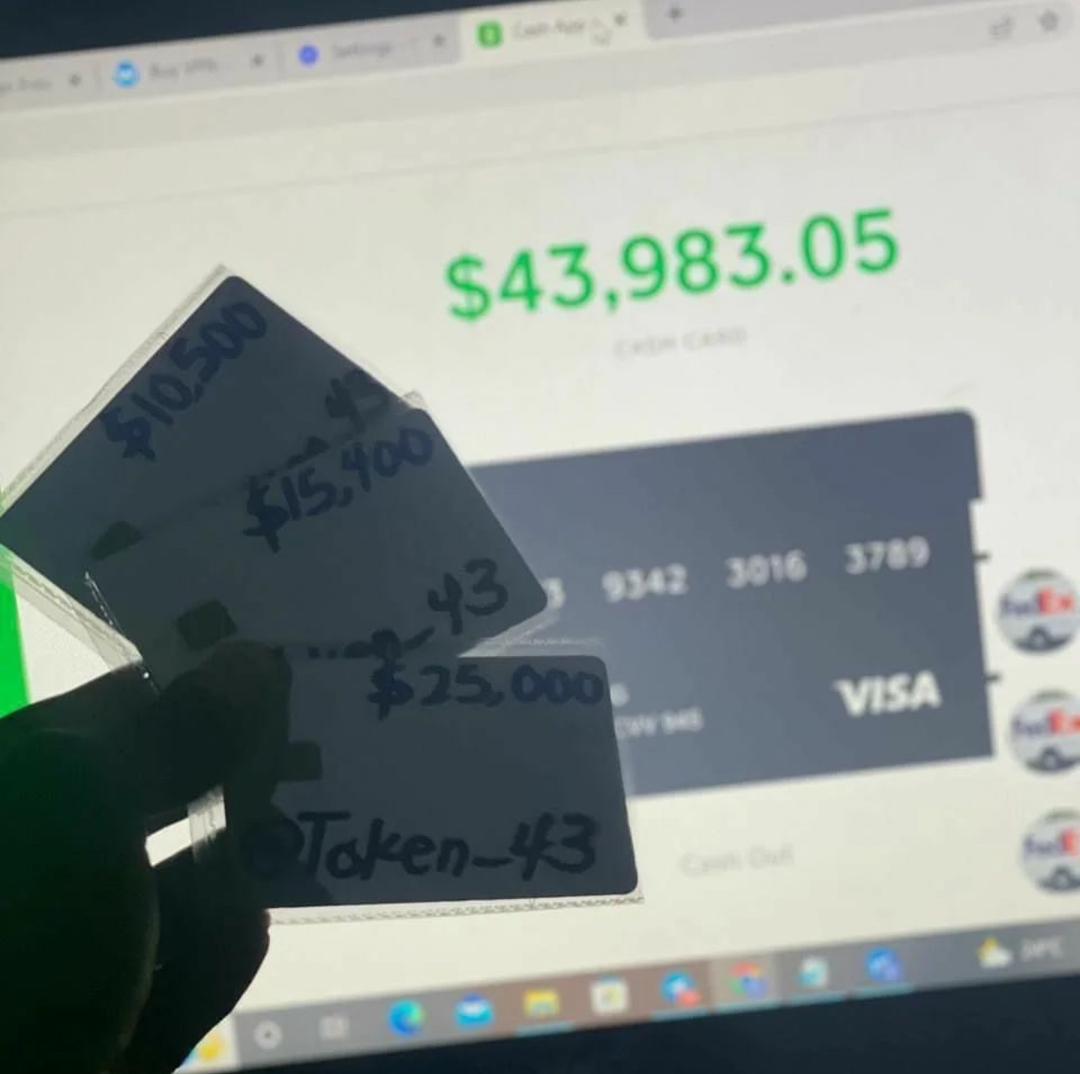
On top of that, some clone cards can be reloaded with additional money, which is beneficial for people who have to have for making Repeated purchases. Clone Cards available for purchase
One of many key attributes of EMV chip cards is their power to produce a novel cryptogram for every transaction, ensuring that the data can not be reused for fraudulent needs. This dynamic authentication approach considerably lessens the chance of unauthorized access to delicate cardholder data, bolstering the overall stability of payment transactions.
⚒️Flexible and customizable: If a tool offers people different options like resizing partitions when copying disks, copying will be much easier in your case.
Alright, let’s say the worst has took place, plus your charge card has fallen sufferer to cloning. Don’t worry – we’ve received a video game approach to assist you to get better.
Various Transactions: Criminals usually maximize using the cloned bank card by conducting numerous transactions in just a shorter time period. This method assists them maximize their fiscal get though reducing the likelihood of detection.
It is vital to consider ways to ensure the security of your respective copyright. Hello there environment. Be sure to preserve the card within a protected locale and never ever share the cardboard number or security code with any individual.
Details Breaches: Hacking incidents can expose your charge card facts if an internet site or a firm’s databases is compromised. Criminals can then offer this information on the click here darkish Internet, the place it can be utilized for credit card cloning.
Moreover, fraudsters might attempt to intercept the interaction concerning the chip plus the terminal, exploiting vulnerabilities to extract important authentication data and replicate it for fraudulent applications.
Never share your card aspects or PIN with any one. Also, be cautious when supplying your individual details online or in excess of the cell phone. Scammers frequently use phishing procedures to get sensitive information and facts.
With regards to securing your online things to do, particularly inside the realm of PHP proxy and SSL connections, ForestVPN gives robust encryption and privateness features. Through the use of ForestVPN, you could be sure that your PHP proxy connections are encrypted, adding an additional layer of security towards prospective threats like eavesdropping or details interception.
It is essential to prioritize cybersecurity and click here just take important precautions to protect personalized financial info. By staying knowledgeable, performing exercises warning, and promptly reporting any suspicious exercise, persons can decrease the chance of slipping victim to charge card cloning and decrease the possible authorized ramifications associated with engaging click here in unlawful pursuits.
A: Clone cards can be obtained from a spread of retailers, both of those online and in-retail outlet. Ensure to match the features and costs related to each card before making a obtain. wherever to buy clone cards.
I study a write-up online about an ATM hacking card which i also give it a check out,And i acquired it from your hacker named Donald Williams final 7 days and now I've